Exploring IEEE 2883 – The Future of Data Sanitization
As our digital landscape evolves at a breakneck pace, safeguarding sensitive information is more critical than ever. Conventional file deletion techniques fail to fully eliminate data, exposing organizations to potential breaches and compliance risks. Enter the IEEE 2883 standard—a comprehensive framework designed to elevate data sanitization. Explore how this international standard empowers organizations to adopt secure and environmentally responsible practices now and in the future.
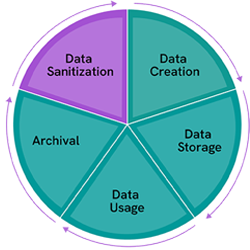
What is Data Sanitization?
The sanitization of data involves using specific methods to ensure it cannot be accessed and recovered.
This critical process addresses the following
- Data Resilience: Storage devices are designed to prevent data loss. This is why simply deleting a file does not mean it’s been eliminated.
- Data Forensics: Advanced tools can recover deleted files, heightening the risk of breaches.
- Compliance Requirements: Many industries demand strict adherence to sanitization protocols and record-keeping.
As the final phase of the data lifecycle, sanitization plays a vital role in preventing breaches and ensuring compliance.
IEEE 2883: A New Benchmark for Data Sanitization
IEEE 2883, introduced in 2022, is an international standard that provides detailed guidance on data sanitization methods. It bridges gaps in older standards, accommodating advancements in storage technology and sustainability.
KEY OBJECTIVES
- Defines what sanitization is and is not
- Enhances data security and privacy
- Aligns with compliance and regulatory demands
- Describes standardized data sanitization methods: Clear, Purge, and Destruct
- Covers media-specific and interface-specific sanitization techniques
- Contains guidance for composite devices like printers, mobile devices, and gaming systems
- Includes sustainability as part of sanitization method decision-making
- Lists upcoming storage technologies to be aware of
Understanding the Sanitization Methods
CLEAR

Definition: Logical techniques that remove data from accessible storage areas, making it unrecoverable through simple methods.
Methods: Formatting or deallocation
PURGE

Definition: Advanced logical or physical techniques that eliminate data, ensuring recovery is infeasible even with state-of-the-art techniques.
DESTRUCT

Definition: Physical destruction that leaves devices permanently unusable.
Methods: Disintegrate, melt, and incinerate
Choosing the appropriate sanitization method involves careful assessment of your organization’s data privacy policies, risk tolerance, and sustainability goals. IEEE 2883 addresses both security demands and environmental considerations.
Verification
How do you know if sanitization worked? IEEE 2883 specifies verification steps based on the sanitization type. For clear or purge, the standard requires confirmation that the command was performed. If the device underwent destruction, verification includes physical inspection of the results.
Documentation
All sanitization events must be documented. IEEE 2883 defers to ISO/IEC 27040 standards. Records should include the following:
- Who performed the sanitization and when/where it was performed
- What equipment and which sanitization method was used: clear, purge, or destruct
- Which sanitization technique was utilized and the result: pass or fail
- What verification was used and the result
- What the final disposition of the media was (example: reused)
Proof of sanitization is generally provided through a certificate of destruction along with a detailed workflow log that includes sanitization, verification, and disposition information.
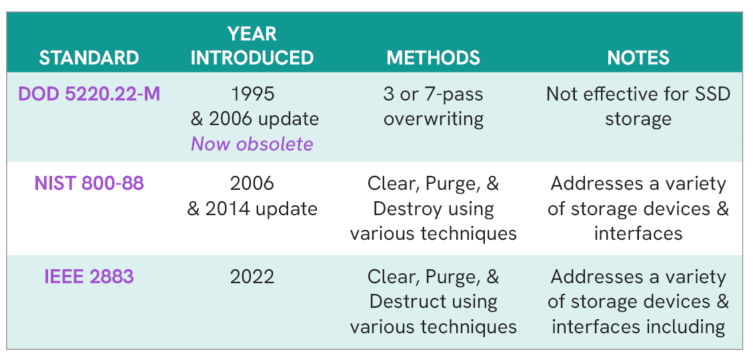
The Evolution of Data Sanitization
A comparison of data sanitization standards from oldest to newest:
A Modern Approach to Data Sanitization
IEEE 2883 addresses numerous challenges that older standards do not.
- NVMe, SAS, SATA storage devices have been further defined and or have expanded features
- HDD and NAND storage (SSD) densities have increased requiring better physical destruction techniques
- Growth in devices with embedded storage (IoT devices, printers, and mobile devices)
- Introduces environmental impact as part of the risk assessment analysis
- Aligns with the ISO/IEC 27040 and is written so there can be compliance with requirements and regulations
- As an international standard, it ensures cross-border regulatory compliance
By addressing emerging technologies while integrating considerations for environmental impacts, IEEE 2883 supports a secure and sustainable digital future.
Final Thoughts
IEEE 2883 sets a new standard for organizations seeking robust, forward-looking data sanitization practices. By aligning with this framework, businesses can enhance security, build trust, and embrace sustainability.
If you have questions about IEEE 2883, please reach out to us.
References
End-to-end deinstallation of desktops, laptops, servers, networking gear, and data center hardware; white-glove onsite teams trained for secure chain of custody initiation.
Secure collection containers and scheduled pickups for enterprise campuses and data centers; flexible container sizes and recurring logistics programs.
GPS tracked transport, serialized item level tracking, secure serialized containers, digital chain of custody documentation, and secure fleet partners vetted for compliance.
NIST 800-88 compliant data erasure, cryptographic wipe, or certified physical media destruction; serialized certificates provided.
Sustainable electronics recycling, e-Stewards certified downstream compliance with local, federal and Basel regulations, responsible material recovery, and transparent reporting. Mass balance accounting of all materials received and dispositioned.
In house refurbishment and resale through global B2B channels, wholesale networks, and Sage-owned retail outlets; maximized equipment value return. Repair and refurbishment services increase the salable value of all assets received.
OEM and distributor trade in program management, valuation services, and turnkey collection for multi vendor hardware environments.
Asset testing, configuration, imaging, and deployment support for newly acquired or redeployed equipment.
Reporting supports timely decommissioning of all licenses installed on assets received.
Mobile shredding units, onsite media destruction, witnessed destruction options, serialized proof, and video verification upon request.
Complete handling of leased asset reconciliation, condition assessment, packaging, documentation, and on time returns to multiple lessors. Repair, refurbishment and kitting services minimize lessor chargebacks at lease termination.
Fully managed equipment or resale revenue donation programs, including data wiping, refurbishment, and nonprofit delivery.
Custom portals and programs enable employees to purchase refurbished corporate devices securely and conveniently with zero enterprise involvement. A one-year warranty is included with all purchases.
Enterprise scale redeployment preparation includes testing, repair, imaging, configuration, repackaging, and global distribution.

.svg)




















